
Designed for one-to-one custom content.
Photos or videos.One client. One delivery. One traceable record.
Register private custom content before sending it to a client.
If the file appears elsewhere, you can confirm which delivery it came from.
Many creators sell private custom photos or videos directly to individual clients.
Once the file is delivered, it can be copied, reposted or redistributed.
Perfinger allows you to register each custom delivery before sending it.
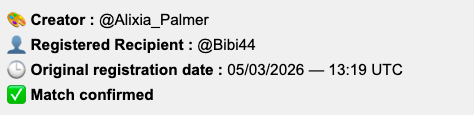
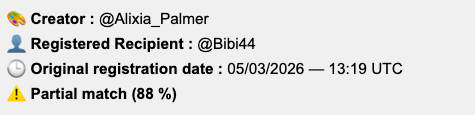
If the same content appears elsewhere later, structural similarity can confirm the match with the registered delivery.
Creating exclusive custom content is real work. Planning. Filming. Lighting. Editing. Sometimes hours for a single custom.
When that content is redistributed for free, it is economic damage.
The biggest problem is not discovering a leak. It is proving where the content originally came from.
You lose:
• Direct revenue
• Perceived exclusivity
• Brand value
• Client trust
And once the file is modified or re-uploaded, traditional file hashes are useless.
Perfinger combines perceptual AI embeddings, structural hashing confirmation, image perceptual fingerprinting frame-by-frame video matching, facial identity validation (ArcFace), and FAISS similarity indexing.
Video confirmation requires ≥70% frame correspondence under strict similarity thresholds.
Watermarks are visible or hidden marks added directly to the media file.
Because they are embedded in the file itself, they are fragile and relatively easy to circumvent.
Watermarks can often be removed or bypassed through:
• CroppingPerfinger does not modify your file and does not embed any visible mark.
Instead, it analyzes the visual structure of the content itself and generates a structural fingerprint.
Because the fingerprint is derived from the visual structure, it remains detectable even if the file is modified.
Resistant to:
Perfinger does not scan the internet.
It does not send DMCA notices.
It does not remove leaked content.
Most leaks are not discovered through monitoring tools.
They are discovered:
• Through screenshots
• Through other creators
• Through private communities
• Through end clients
When a leak becomes known, what matters is not how it was found. What matters is whether you can prove who it came from.
Perfinger creates a structured record linking:
• The creator
• The exclusive custom
• The single recipient
If the same content appears publicly, Perfinger allows similarity analysis against the registered delivery.
When content is untraceable, leaking feels risk-free.
When content is registered and traceable, leaking becomes a personal risk.
Perfinger does not try to “catch pirates”. It transforms each custom into a traceable transaction.
And that changes the dynamic between creator and buyer.
Before sending a custom photo or video to a client, you register the final version inside Perfinger.
The system generates a unique structural fingerprint of the visual content.
The system generates:
• Perceptual fingerprint generation
• Secure timestamp creation
• Unique identifier assignment
• Cryptographic signature (Ed25519)
For videos, multiple frames are extracted and compared.
The file may change. The visual identity remains.
The registered file is linked to:
• The creator
• The custom content
• The specific recipient
Before delivery, you inform the buyer:
When content is untraceable, leaking feels anonymous.
When content is registered, leaking becomes a personal risk.
Perfinger is not:
• A watermarking tool
• A mass distribution tracker
• An internet monitoring service
• A piracy removal system
It is a documentation and accountability system for exclusive one-to-one content.
Perfinger applies strict similarity verification for both images and videos.
For images involving people, facial identity consistency is verified.
For video analysis, detection requires:
• Frame similarity ≥ 0.995
• ≥70% matching frames
• Duration tolerance within 10%
No match means no exposure of original metadata.
Perfinger allows you to document content before delivery, and later confirm similarity even after modifications.
Below is an example workflow showing how a registered delivery can later be matched against a leaked or reposted version.

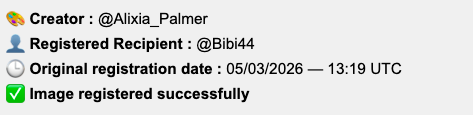


These documents provide structured proof that a specific content file was registered before delivery.
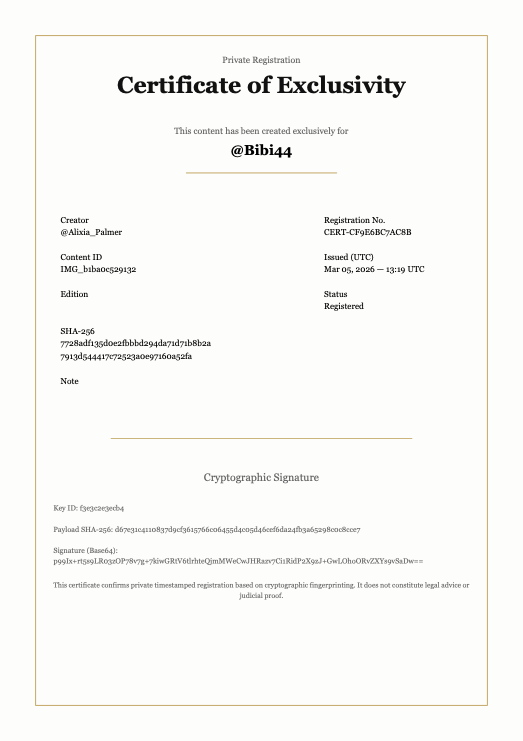
Includes unique content ID, timestamp, file hash and cryptographic signature.
Signals that the content is formally documented.
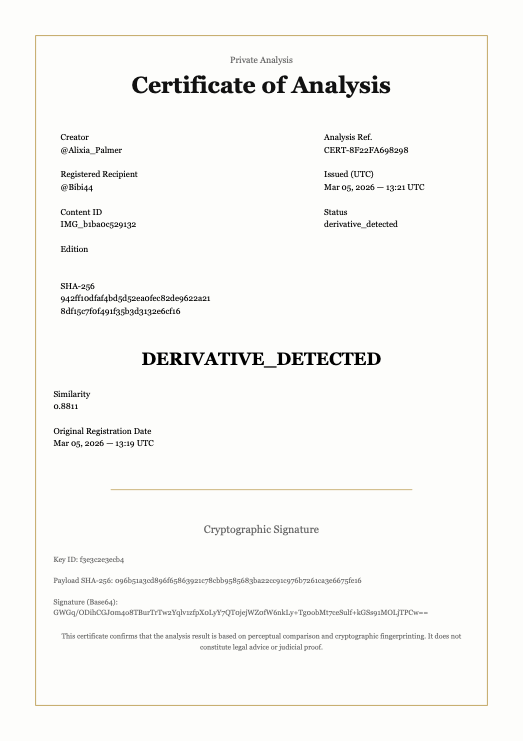
Generated when suspicious content is analyzed.
Displays similarity score and structured comparison data.
No content is hosted or distributed.
Only encrypted signatures and metadata.
Optimized for premium custom creators.
Payments are securely processed by Stripe.
Subscriptions can be canceled at any time.